Smartphones have become an essential part of our daily lives. From communication and banking to entertainment and productivity, these devices hold a wealth of personal information. However, with the increasing reliance on smartphones, it’s crucial to prioritize their security.
This article explores the best practices for smartphone security, helping you safeguard your personal data and protect yourself from potential mobile threats too.
Understanding the Importance of Smartphone Security

Before delving into the best practices, it’s important to comprehend why smartphone security matters. Neglecting smartphone security could result in dire consequences, ranging from identity theft to financial loss. With billions of smartphones in circulation worldwide, cybercriminals are relentless in their pursuit of exploiting vulnerabilities and gaining unauthorized access to personal data.
In today’s interconnected world, where smartphones have become an extension of ourselves, it is crucial to recognize the significance of securing these devices. Smartphones are no longer just a means of communication; they have evolved into powerful tools that handle a wide range of tasks. From personal communication to online banking, smartphones have become an integral part of our daily lives.
The Risks of Neglecting Smartphone Security
By neglecting smartphone security, you leave yourself vulnerable to a variety of risks. These include:
- Data breaches: Personal information, including passwords and financial details, can be accessed by hackers. This can lead to severe consequences, such as unauthorized access to bank accounts or sensitive personal information.
- Identity theft: Cybercriminals can use stolen information to impersonate you or commit fraudulent activities. They can open credit accounts in your name, make unauthorized purchases, or even ruin your credit score.
- Malware attacks: Malicious software can be installed on your smartphone, compromising its functionality and compromising your data. Malware can steal sensitive information, track your online activities, or even take control of your device.
- Phishing attempts: Cybercriminals may send deceptive messages or emails to trick you into revealing sensitive information. These phishing attempts can lead to the theft of your login credentials, passwords, or other personal information.
The Role of Smartphones in Our Daily Lives
As smartphones have become an integral part of our lives, understanding their role is crucial to grasp the significance of securing them. From personal communication to online banking, smartphones handle a wide range of tasks.
Additionally, smartphones often store personal photos, videos, and documents, ensuring that any compromise could have severe consequences for your privacy and security.
Smartphones have revolutionized the way we communicate, work, and access information. They have become our primary source of communication, allowing us to stay connected with friends, family, and colleagues no matter where we are. Moreover, smartphones have transformed the way we access information, providing us with instant access to the internet and a vast array of apps and services.
With the increasing reliance on smartphones, it is essential to recognize the potential risks and take proactive measures to secure our devices. By implementing strong security practices, such as using strong passwords, enabling two-factor authentication, and keeping our mobile devices up to date with the latest software updates, we can minimize the risks and protect our personal information.
Setting Up Mobile Devices for Maximum Security

To ensure the highest level of security for your smartphone, it’s essential to follow best practices when setting it up.
When it comes to securing your smartphone, there are several steps you can take to protect your personal information and sensitive data. In addition to the basic setup process, there are additional measures you can implement to enhance the security of your mobile device.
Choosing a Strong Password
A strong password is key to keeping your smartphone secure. Avoid common passwords such as “123456” or “password” and opt for complex combinations of letters, numbers, and symbols. It’s important to choose a password that is unique and not easily guessable. Consider using a combination of uppercase and lowercase letters, along with special characters to make it even more secure.
In addition to choosing a strong password, it’s crucial to enable the option to lock your smartphone after a certain period of inactivity. This feature ensures that even if someone gains physical access to your device, they won’t be able to access your data without entering the password.
Enabling Biometric Security Features
Most modern smartphones come equipped with biometric security features such as fingerprint scanners or facial recognition. These features provide mobile users with an additional level of protection, ensuring that only you can unlock your device.
Enabling biometric security features not only adds convenience to the unlocking process but also enhances the security of your smartphone. Biometric data, such as your fingerprint or facial features, is unique to you, making it difficult for unauthorized individuals to gain access to your device.
It’s important to note that while biometric security features are highly secure, they are not foolproof. In some cases, they can be bypassed using advanced techniques. Therefore, it’s always recommended to have a strong password set up as a backup security measure.
Setting up your smartphone for maximum security involves choosing a strong password, enabling the option to lock your device after a period of inactivity, and utilizing biometric security features. By following these best practices, you can ensure that your personal information and sensitive data remain protected from unauthorized access.
Essential Security Settings and Features
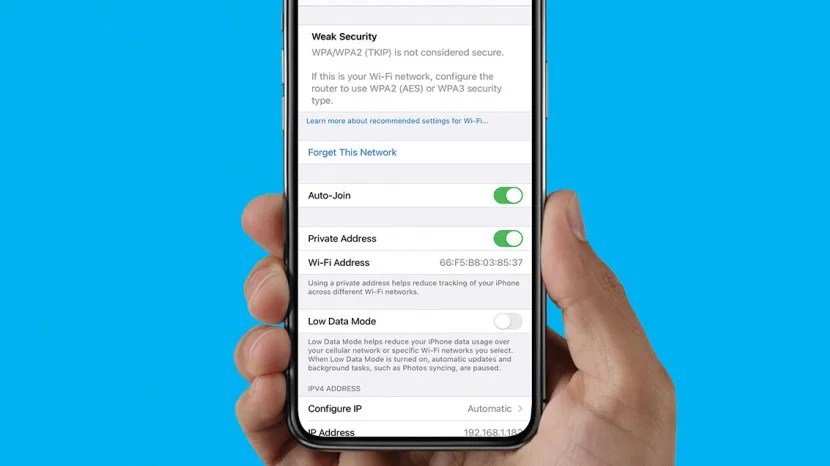
In addition to the initial setup, there are several essential security settings and features that should be enabled on your smartphone.
Your smartphone is not just a device for communication and entertainment; it holds a wealth of personal information, from sensitive emails and financial transactions to personal photos and videos. Therefore, taking steps to protect your smartphone’s security is of utmost importance.
Regular Software Updates
Regularly updating your smartphone’s software is crucial in maintaining its security. Manufacturers release updates to address vulnerabilities and patch potential security loopholes. These updates not only enhance the functionality of your mobile device security but also ensure that it remains protected against the latest threats.
By installing software updates promptly, you are taking proactive measures to safeguard your smartphone from potential attacks. Ignoring these updates exposes your device to unnecessary risks, leaving it vulnerable to hackers and malware.
Furthermore, software updates often come with new features and improvements that enhance the overall user experience. So, not only are you enhancing your smartphone’s security, but you are also benefiting from the latest advancements in technology.
Encryption and VPNs
Encrypting your smartphone’s data adds an extra layer of protection, ensuring that in the event of theft or unauthorized access, your data remains unintelligible. Encryption scrambles your phone’s operating system and data, making it unreadable without the encryption key, which only you possess.
Modern smartphones come equipped with built-in encryption features that you can easily enable. By encrypting your device, you are safeguarding your personal information, such as contacts, messages, and files, from falling into the wrong hands.
Additionally, using a Virtual Private Network (VPN) when connecting to public Wi-Fi networks protects your data from potential eavesdroppers. Public Wi-Fi networks, such as those found in coffee shops, airports, and hotels, are often unsecured, making it easier for hackers to intercept your data.
A VPN creates a secure and encrypted connection between your smartphone and the internet, ensuring that your online activities remain private and protected. It acts as a shield, preventing anyone from monitoring your internet traffic or stealing sensitive information.
By utilizing encryption and VPNs, you are taking proactive measures to safeguard your smartphone’s security and protect your personal information from unauthorized access.
Safe Usage of Public Wi-Fi Networks

Public Wi-Fi networks can be convenient but pose significant security risks. It is important to understand the dangers associated with using public Wi-Fi and take necessary precautions to protect your sensitive information.
The Dangers of Public Wi-Fi
Public Wi-Fi networks are often unsecured networks, making it easier for hackers to intercept your data. When connected to a public Wi-Fi network, your online activities and sensitive information can be exposed. This includes passwords, financial details, and personal communications.
Imagine you are sitting in a coffee shop, enjoying a cup of your favorite brew while browsing the internet on your laptop. Little do you know that a cybercriminal sitting a few tables away is secretly monitoring your online activities. Without proper security measures, your personal information is at risk of being stolen.
Public Wi-Fi networks are a breeding ground for hackers. These networks are usually open and lack encryption, which means that any data transmitted between your device and the network can be easily intercepted. Hackers can use various techniques, such as packet sniffing, to capture your sensitive information without you even realizing it.
Once a hacker gains access to your data, they can use it for malicious purposes. They may steal your identity, access your bank accounts, or even sell your information on the dark web. The consequences of falling victim to such attacks can be devastating, both financially and emotionally.
Using a VPN on Public Networks
Utilizing a Virtual Private Network (VPN) on public Wi-Fi networks is one of the most effective ways to protect your online privacy and security. A VPN creates a secure and encrypted connection between your device and the internet, ensuring that your data remains private and inaccessible to hackers.
When you connect to a public Wi-Fi network and activate a VPN, all of your internet traffic is encrypted. This means that even if a hacker manages to intercept your data, they won’t be able to decipher it without the encryption key. It’s like sending your information through a secure tunnel, shielding it from prying eyes.
Moreover, a VPN masks your IP address, making it difficult for anyone to track your online activities. This adds an extra layer of anonymity and protects your identity from being exposed.
Using a VPN is particularly crucial when accessing sensitive information or conducting financial transactions on public Wi-Fi networks. Whether you are checking your bank account balance, making online purchases, or logging into your email, a VPN ensures that your data remains secure and confidential.
Look for a VPN service that offers strong encryption, a strict no-logs policy, and a wide range of server locations. Additionally, keep your VPN software up to date to ensure you have the latest security patches.
By using a VPN on public Wi-Fi networks, you can browse the internet with peace of mind, knowing that your data is protected. Don’t let the convenience of public Wi-Fi networks lure you into a false sense of security. Take the necessary precautions and prioritize your online privacy and security.
Protecting Personal Information on Smartphones
Smartphones have become an integral part of our lives, serving as a repository for an abundance of personal information. From contact details and photos to banking and social media accounts, our smartphones hold a treasure trove of sensitive and private data. With this in mind, it is imperative to implement robust security measures to safeguard our personal information from unauthorized access and potential misuse.
Privacy Settings and Permissions
One of the first steps in protecting personal information on smartphones is to review and adjust the privacy settings. By doing so, you can limit the access that apps have to your personal information. Take the time to go through each setting, ensuring that you are comfortable with the level of access granted to different applications.
Furthermore, it is crucial to scrutinize the permissions requested by each app. While some permissions may be necessary for the app’s intended functionality, others may seem excessive or unnecessary. Take a moment to question why a particular app requires access to certain aspects of your personal information. If you feel uncomfortable with the permissions requested, consider finding an alternative app that respects your privacy preferences.
Securely Storing Sensitive Data
Encrypting and securely storing sensitive data is paramount in protecting your personal information. Utilizing encrypted cloud storage services or password-protected applications can provide an added layer of security for confidential documents and files. By encrypting your data, you ensure that even if your smartphone falls into the wrong hands, the information stored within remains inaccessible to unauthorized individuals.
When choosing a cloud storage service, opt for reputable providers that prioritize data security and offer robust encryption protocols. Additionally, consider using password-protected applications for storing sensitive information, such as financial records or personal documents. These applications often employ advanced encryption algorithms to safeguard your data from potential breaches.
It is also worth noting that regularly backing up your smartphone’s data is essential. In the event of a lost or stolen device, having a recent backup ensures that you can restore your personal information onto a new device without compromising its security.
Keeping Software and Operating System Up to Date
Regularly updating your smartphone’s operating system and applications is crucial in maintaining a secure environment for your personal information. Software updates often include security patches and bug fixes that address vulnerabilities discovered by developers or security researchers. By keeping your software up to date, you minimize the risk of potential exploits that could compromise the security of your personal information.
Enable automatic updates on your smartphone to ensure that you receive the latest security patches as soon as they become available. Additionally, be cautious when downloading and installing applications from third-party sources, as they may not undergo the same rigorous security checks as those available through official app stores.
By following these best practices, you can significantly enhance the security of your personal information on smartphones. Remember, the value of your personal data cannot be understated, and taking proactive steps to protect it is essential in today’s digital landscape.
Dealing with Lost or Stolen Smartphones

Despite taking precautions, there is always a risk of losing or having your smartphone stolen. Losing a smartphone can be a frustrating and stressful experience, but there are steps you can take to protect yourself and increase the chances of recovering your device.
One of the first things you should do if you lose your smartphone is to remotely lock and wipe your device. Most smartphones have built-in features that allow you to do this. By remotely locking your device, you can prevent unauthorized access to your personal information. This is especially important if you have sensitive data, such as banking or credit card information, stored on your phone.
In addition to locking your device, you can also remotely wipe your smartphone. This means that all the data on your phone will be erased, ensuring that no one can access your personal information. However, it’s important to note that once you wipe your device, you won’t be able to recover any data that was stored on it.
When you lose your smartphone, it’s important to report it to your mobile service provider and local authorities. By reporting the loss, you increase the chances of recovering your device and minimizing the potential risks associated with the loss. Your mobile service provider can help track your device and may be able to disable it to prevent unauthorized use.
When reporting a lost or stolen mobile phone, make sure to provide your mobile service provider and local authorities with all the necessary details. This includes the make and model of your device, the IMEI number, and any other identifying information. The more information you provide, the better the chances of recovering your smartphone.
In some cases, you may also want to consider contacting your insurance provider if you have smartphone insurance. They can guide you through the process of filing a claim and potentially getting a replacement device.
It’s important to remember that losing a smartphone can happen to anyone, and it’s not a reflection of your personal responsibility. However, by taking proactive steps such as remotely locking and wiping your device, reporting the loss, and providing all the necessary details, you can increase the chances of recovering your smartphone and protecting your personal information.
The Future of Smartphone Security
As technology evolves, so do the threats to smartphone security. Staying informed about emerging mobile security technologies and new threats is vital.
Emerging Mobile Device Security Technologies
Biometric advancements, such as iris scanning and voice recognition, are on the horizon, promising enhanced security measures. Additionally, developments in artificial intelligence and machine learning can help identify and prevent potential mobile security threats and breaches.
Staying Informed About New Threats
Cybercrime is an ever-evolving landscape, with new threats emerging regularly. Keeping up with the latest news and security developments ensures you stay one step ahead of potential attackers.
In conclusion, adhering to best practices for smartphone security is essential in safeguarding your personal data and protecting yourself from cyber security threats everywhere. By understanding the potential risks, adopting secure setup practices, utilizing essential security settings, and staying vigilant, you can enhance your smartphone’s security and enjoy the benefits of modern technology without compromising your privacy or safety.
